From time to time we hold internal courses on technical topics in order to increase the general knowledge of our [… Read more]
LA1K / LA100K / LA1UKA
Month: November 2017
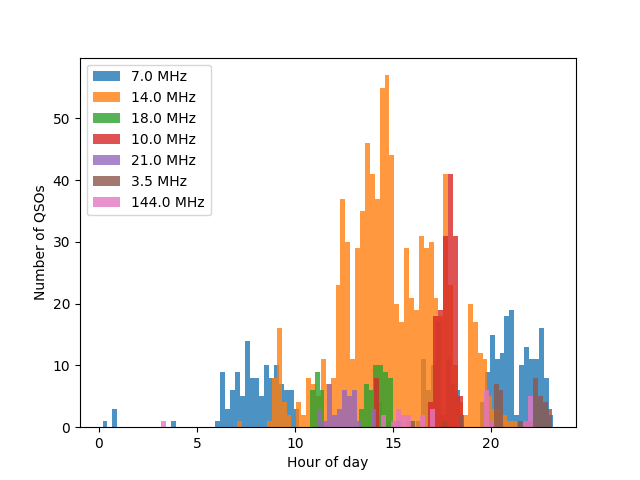
Telefonitesten (Norwegian: the Telephony Test) is a Norwegian-only Ham Radio competition occurring every fall. ARK has a tradition of participating [… Read more]
UKA-17 is over, and LM100UKA is no more. As a part of the series, “LA3WUA and LA9SSA discover that Python [… Read more]
The UKA festival is finally over, and we are back to normal here at the club. It has been a [… Read more]
LA1K is always interested in working new DXCCs. To assist with this we wanted to see if we could make [… Read more]
© 2024 Akademisk Radioklubb
Theme by Anders Norén — Up ↑