After our first post about the Maestro “hack” , we received quite a bit of attention towards our project. Particularly, there were a number of requests for revealing the backdoor into the Maestro software. In this post we will finally reveal said backdoor, and share some of the hardware and software specs we could gather from looking inside the operating system.
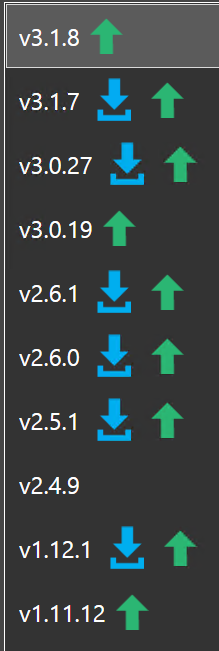
We would like to clarify some things before revealing the backdoor; we are running on a older version of the Maestro-software, 2.4.9, which might be the reason that we are able to implement this modification. We haven’t tested this on other versions, so your results may vary.
There are also multiple hardware revisions of the Maestro released, and this modification might only be applicable to our specific model. Please keep in mind that even though we have gained access into the device locally, this does not necessarily mean your device is accessible just by being connected to the Internet. On the other side we can’t confirm that the device is secured properly either, so we definitely welcome any insight into the security aspects of the Maestro-panel.
We would like to specify that we have in no way developed any software for accessing the device, and that our testing (and additional software) has solely been possible through a number of commands and tricks, without any third-party software. If you don’t feel comfortable using the command prompt and looking for solutions on Google, we would probably advice not to try this on your own Maestro as you could potentially brick your device. We take no responsibility for any failed attempts to recreate the following procedure.
Gaining access to the system
To start off, we recommend connecting your Maestro to a Internet-free network. This can be a spare wireless router, connected either wirelessly or via an Ethernet-cable, but the network should be without Internet-access. This will be explained later on, but the main goal here is to interrupt a web request from the embedded web-browser in the Maestro software.
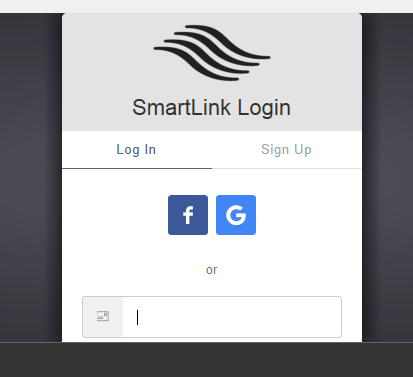
When connected to your network, press the “Log In”-button to sign into your Flex-account. Since the device has an IP-adress, but can’t reach the Internet, it will show a white screen while trying to resolve the domain name for the Flexradio-site.

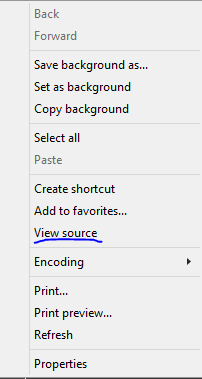
And here is the trick: if you touch and hold the screen to initiate a right click while this page loads, a option menu will pop up. If you press “View source”, you will be launched into Notepad where you can see the contents of the current page.
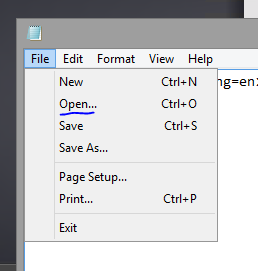
From this Notepad-window you are then also able to launch Windows Explorer by pressing Open in the File-menu.
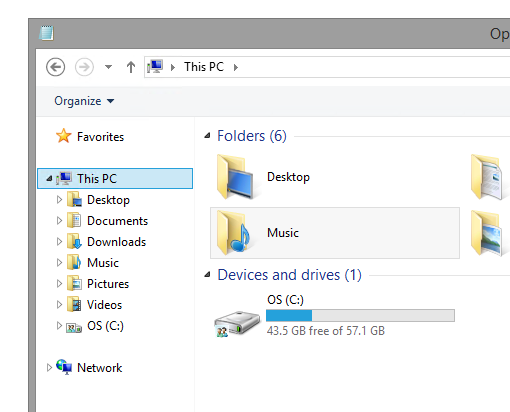
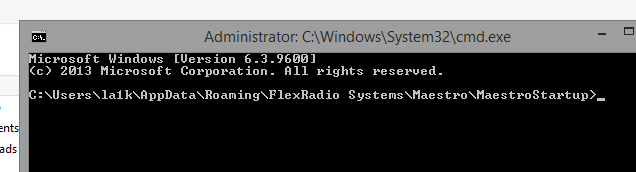
If you know anything about Windows you might know that you can type pretty much anything into the top address bar, besides browsing the system drive. By launching the command prompt (simply typing “cmd”), you have a way of starting additional programs and the rest of the journey is up to you.
If you don’t connect your radio to a network at all, you will automatically be forwarded to a offline page which doesn’t allow right click.
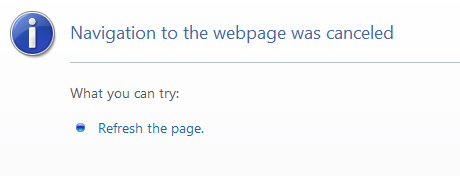
On the other hand, if you connect your radio to a network with Internet-access, the time between pressing “Log In”-button and the site actually loading could be quite short depending on your Internet-connection. Attempts this way can prove to be difficult, but they are definitely possible.
Hardware information
Before attempting to load additional software into the Maestro, we wanted to check that the hardware would actually support our programs. Luckily it runs a standard x86 platform with support for most Windows-compatible software. It is built upon a Dell tablet, which is probably the main contributor for the large 7″ touch-display in front of the unit. This contains a Intel Atom quad-core CPU, 2GB of RAM, and a relatively large 64GB SSD. With this in mind, we felt safe putting additional software on the device.
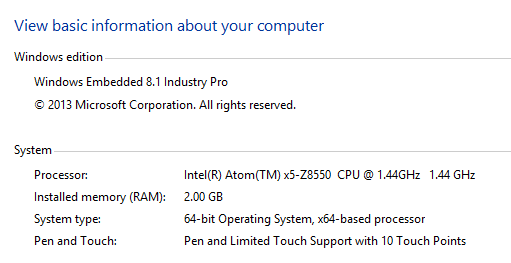
The device runs Windows 8.1 Embedded, a special edition of Windows which is made for industrial equipment. The embedded versions of Windows usually have lower maintenance requirements, compared to the traditional editions of Windows found on desktop computers and such. These operating systems come stripped of any unnecessary software, which means manufacturers are able to ship it only with the programs needed.
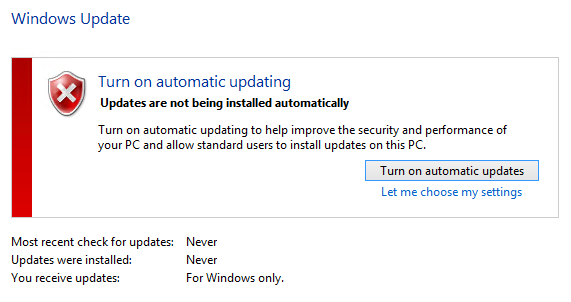
Another option manufacturers usually configure for similar systems is disabling certain parts of Windows Update (like automatic restarts), which is supposedly what Flex has done here. This is possibly to avoid any potential bugs caused by unsupported updates. We are somewhat skeptical to running a device without applying any updates, but can’t really speak any further for the security of the device as we are not experts by any means.
A plausible scenario could be that Flex are installing security updates through some other means (like the Maestro-software). If someone with more in-depth security knowledge decided to implement the backdoor on their own device, we would definitely be interested to learn about their insights into these design choices.
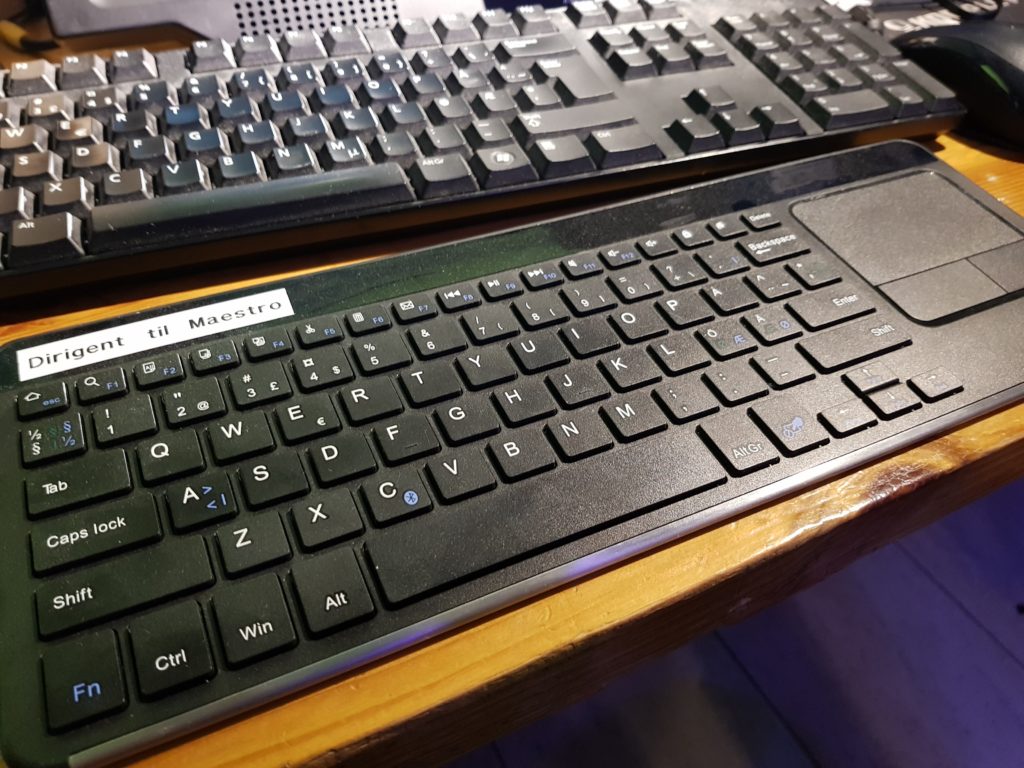
By using the built-in Bluetooth adapter, we have added a Bluetooth keyboard/mouse that allows for easier navigation. We have also enabled Remote Desktop access and created a samba-share from the OS-drive, allowing us to both log into and transfer files to the device remotely.
Lastly, we would like to clarify that this is not exactly a major modification of the device, but it opens up for people to create scripts and software for the device to enable other functionality. Since the device has a Bluetooth-adapter, using a Bluetooth enabled headset could be possible and enable a even more wire-free radio experience. Regardless, we hope that this backdoor comes in handy for others, and that we can see more projects involving the Maestro.
Happy hacking!


Thank you guys, flex needs to also be thankful. Keep digging.
You can get the same access perhaps a bit easier. On my 6600M, Go to the Menu, Frontend, then choose “Display Advanced”. That launches an intel video card configuration utility. The support tab of that has clickable links. You can choose one of them and it will open Internet Explorer. From there you can proceed a few ways. The easiest seems to be click in the header and turn on the menu bar, then you can “file open” from there. Or, like you did “view source” on nearly any page and open up Notepad.
No need to “hide” your internet connection!
Hi Stephen,
Have you been able to get a Bluetooth mouse working with your 6600M?
Manuel W4SSB
Running WSJT also on Maestro would be just as convenient as running Marcus Roskosch’s SmartSDR for IOS on iPad or iPhone. In that version of SmartSDR you could run FT8 for example alongside the main program. The same thing on Maestro would be very desirable!